Since October 2022 Softline has been operating under the brand name Noventiq.
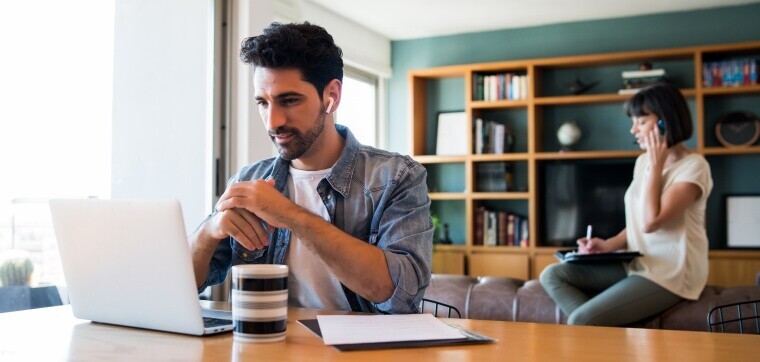
The companies’ challenge is nowadays to provide their employees the infrastructure to work remotely, with safety and security in mind. Microsoft has several solutions for remote work, we collected some of them in a previous article. In this article we introduce you Microsoft Azure AD Application Proxy Service, that provides single sign-on (SSO) and secure remote access to on-premises web applications.
With Azure AD Application Proxy employees can access on-premises applications in the same way they access Office 365 integrated with Azure AD. Azure AD Application Proxy provides secure and efficient access to corporate applications remotely on any device.
Why to use Application Proxy?
It is easy to use because users have a single interface for authentication, the organization doesn’t need to customize or update its applications to provide remote access.
It is safe because the company doesn’t need incoming connections through the firewall to provide users with remote access. When publishing an application using the Azure AD proxy application, it has access to the security analytics tools and authorization controls provided by Azure.
It is cost-effective because Application Proxy runs in the cloud, which makes it easy to use, saving time and money. To use Application Proxy, the network infrastructure doesn’t need to be changed or install additional appliances in the company’s on-premises environment.
What is Application Proxy and how it works?
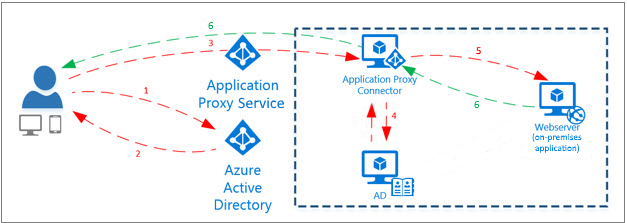
Application Proxy is a feature of Azure AD that enables users to access on-premises web applications from a remote client. Application Proxy includes both the Application Proxy service, which runs in the cloud, and the Application Proxy connector, which runs on an on-premises server. Azure AD, the Application Proxy service, and the Application Proxy connector work together to securely pass the user sign-on token from Azure AD to the web application.
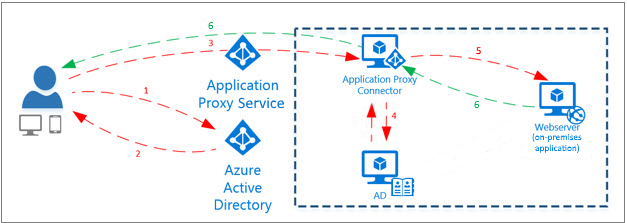
After the user has accessed the application through an endpoint, they are directed to the Azure AD sign-in page. Following the successful sign-in, Azure AD sends a token to their client device. The client sends the token to the Application Proxy service, which retrieves the user principal name (UPN) and security principal name (SPN) from the token. Application Proxy then sends the request to the Application Proxy connector. If you have configured single sign-on, the connector performs any additional authentication required on behalf of the user. The connector sends the request to the on-premises application. The response is sent through the connector and Application Proxy service to the user.
Softline helps your company to implement Azure AD Application Proxy into your IT system. We publish selected business web application on Azure Application Proxy.